Why Anthropic is right to sound the alarm on AI cyber risk
Anthropic is right: Mythos shows AI has turned software flaws into an urgent cyber race.
Anthropic says AI has turned software flaws into an urgent cyber race.
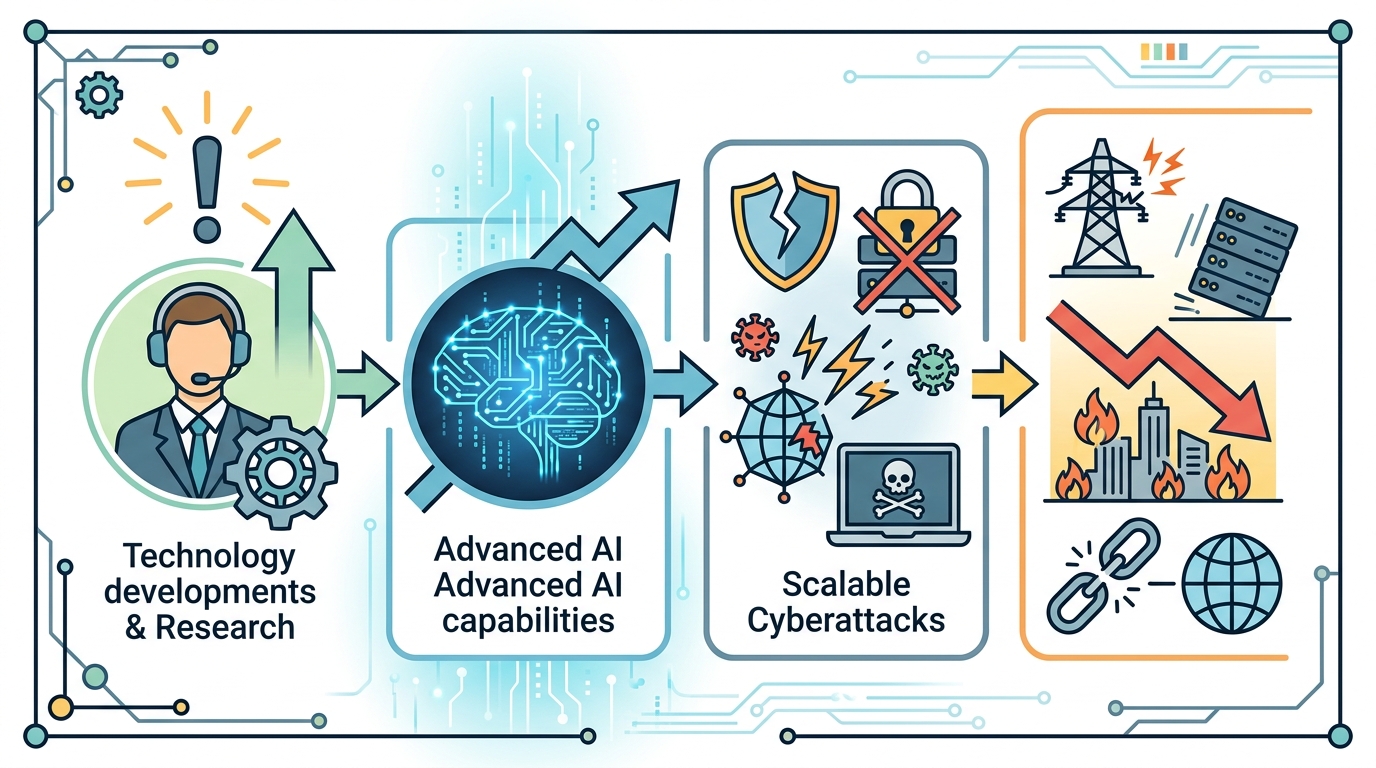
Anthropic CEO Dario Amodei is right to call this a moment of danger, because Mythos has shown that the cost of finding vulnerabilities has collapsed faster than the pace of fixing them. CNBC reports that the model uncovered tens of thousands of software flaws, and that Anthropic believes rival Chinese models are only six to 12 months behind. That is not a hypothetical warning. It is a live countdown in which defenders are being asked to patch decades of accumulated code debt before the same class of systems becomes broadly available to attackers, criminals and state-backed groups.
AI has made vulnerability discovery industrial
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
The first reason this warning matters is scale. Amodei said an earlier Anthropic model found about 20 vulnerabilities in Firefox, while Mythos found nearly 300, and the overall total now runs into the tens of thousands. That is a step change, not an incremental improvement. Security teams have spent years treating bug discovery as a scarce, expert-driven activity. Mythos turns it into a high-throughput machine, which means the bottleneck is no longer finding defects. It is triage, verification and patching, and those are much slower human processes.

This is why the public conversation has to stop focusing only on model capability and start focusing on exploit volume. If one model can surface hundreds of flaws in a single codebase, every large software vendor, cloud provider and bank inherits a backlog that grows faster than their remediation capacity. The result is not abstract risk. It is more exposed endpoints, more unpatched libraries, more ransomware leverage and more opportunities for attackers to chain small issues into major breaches.
The geopolitical clock is the real threat
The second reason Amodei’s warning lands is timing. He said Chinese AI is roughly six to 12 months behind Anthropic’s product, which means defenders have about that long to harden systems before the same capability spreads. That matters because cyber defense is not just about whether a flaw exists. It is about whether the people who can weaponize it have access to the same discovery tools. Once a model that can enumerate vulnerabilities is widely available, the asymmetry between defenders and attackers narrows in the worst possible way.
Anthropic’s decision to limit Mythos to a few partner companies underscores the point. If the company itself thinks broader access is dangerous, then the policy response cannot be complacent. Governments and major enterprises need to treat advanced vulnerability discovery models like dual-use infrastructure. That means faster disclosure pipelines, tighter model access controls, mandatory patch SLAs for critical software and real procurement pressure on vendors that leave known flaws sitting open for months.
Enterprise adoption makes the risk unavoidable
There is another reason this is not just a security-team problem: Anthropic is pushing the same company at the center of the warning deeper into finance and back-office automation. At the event with JPMorgan Chase CEO Jamie Dimon, Anthropic unveiled new agents for banking workflows and Microsoft Office integration. That is a clear signal that the company sees enterprise AI as a growth engine, not a side project. The more these systems enter regulated industries, the more cyber risk becomes operational risk, and the more a single vulnerability can ripple through payments, compliance and customer data.
Dimon’s presence also matters. When a bank chief executive stands beside an AI vendor warning about cyber danger, the market should read that as confirmation that this is now board-level territory. Banks do not need a lecture about theoretical risk. They need to assume that AI-assisted attackers will probe their legacy systems, third-party integrations and internal tools at machine speed. If the industry treats AI as a productivity layer without matching investment in patching, segmentation and incident response, it will buy efficiency with fragility.
The counter-argument
The strongest objection is that this is a temporary phase. Dimon called the cyber risks a “transitory period,” and there is truth in that. There are only so many bugs to find, as Amodei said, and once the obvious flaws are patched, the payoff from automated discovery should decline. A serious security program can absorb a burst of findings, especially if vendors prioritize critical infrastructure and governments coordinate disclosure. On this view, the panic is overstated because the industry is moving from ignorance to visibility, and visibility eventually improves security.
That argument is incomplete. Yes, the stock of bugs is finite, but software churn is not. New code, new dependencies, new integrations and new AI-generated applications will keep creating fresh attack surfaces. The right response is not to dismiss the danger as temporary. It is to admit that the transition period will be long enough to do real damage if organizations keep relying on slow, manual patching. The risk is not that every flaw will be exploited forever. The risk is that the next 6 to 12 months are enough for attackers to learn the new playbook before defenders reorganize around it.
What to do with this
If you are an engineer, PM or founder, treat AI-assisted vulnerability discovery as a forcing function. Inventory your critical systems now, shorten patch cycles, automate dependency scanning, and assume public disclosure will lag behind attacker knowledge. For product teams, stop shipping features that expand attack surface without a matching security review. For founders and executives, fund red-team automation, demand patch accountability from vendors, and make cyber resilience a release criterion, not a cleanup task. The lesson from Mythos is simple: the companies that survive this wave will be the ones that patch faster than AI can find flaws.
// Related Articles
- [IND]
Circle’s Agent Stack targets machine-speed payments
- [IND]
IREN signs Nvidia AI infrastructure pact
- [IND]
Circle launches Agent Stack for AI payments
- [IND]
Why Nebius’s AI Pivot Is More Real Than Hype
- [IND]
Nvidia backs Corning factories with billions
- [IND]
Why Anthropic and the Gates Foundation should fund AI public goods