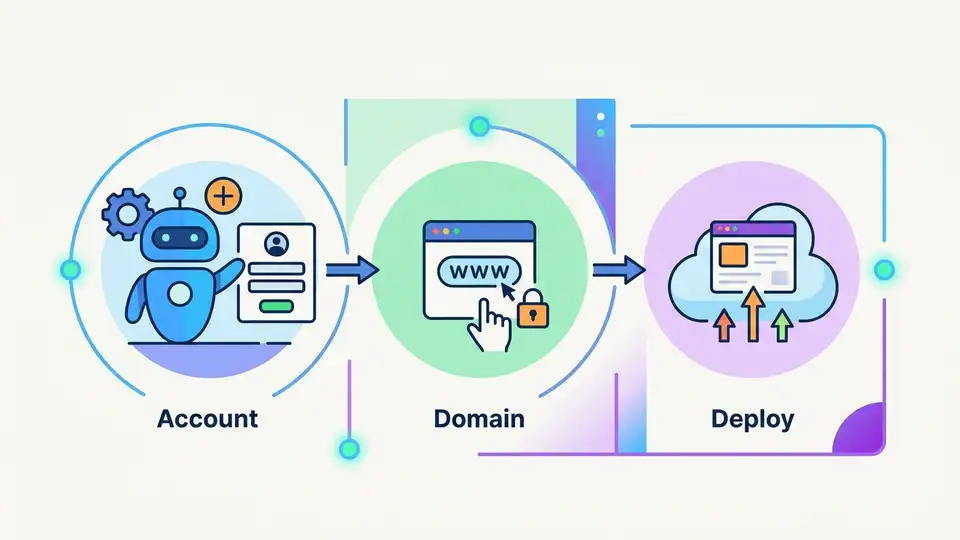
Why agents should be able to create accounts, buy domains, and deploy
First argument: the current setup process is the real product tax
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
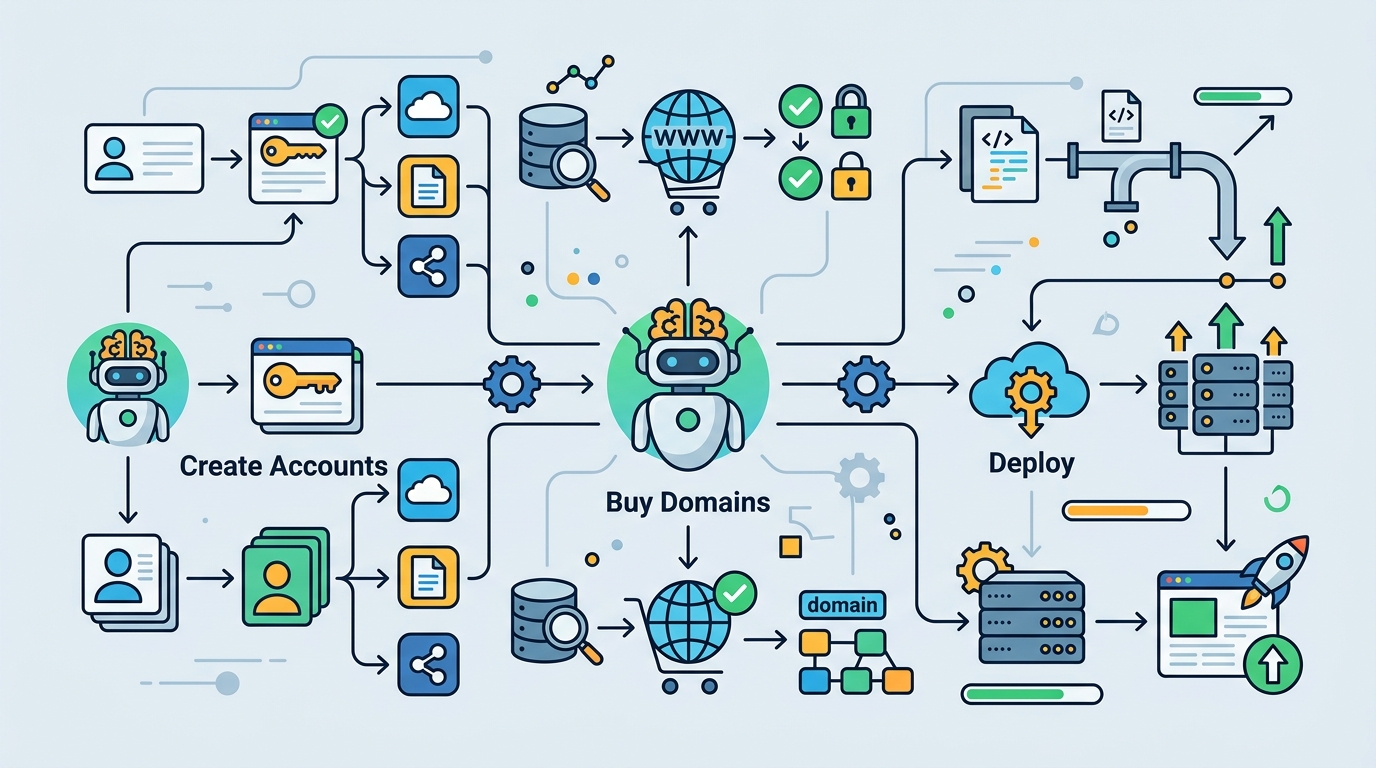
Modern software teams do not lose time writing code first. They lose time on provisioning. A developer can have a working prototype in an hour and still spend the rest of the day creating accounts, verifying email addresses, adding billing, generating tokens, and wiring together the deployment path. Cloudflare’s example shows the agent doing the work humans used to do manually, which means the agent is not replacing the builder. It is replacing the dead time between idea and launch.
That matters because every extra step in onboarding creates abandonment. If a user has to understand which provider owns which service, where the domain lives, how billing is attached, and which token goes where, many will stop before the app is live. Cloudflare’s protocol shifts that burden into discovery, authorization, and payment handled through machine-readable flows. The practical result is simple: the path to production becomes a single transaction, not a tutorial.
Second argument: standards beat one-off integrations
Cloudflare is right to frame this as a protocol problem. Without a standard, each agent-to-platform integration becomes a custom project, which means every new provider repeats the same engineering work: auth, billing, account linking, and permission handling. That does not scale. The blog’s comparison to OAuth is apt, because OAuth succeeded precisely by making delegation reusable instead of bespoke. A similar layer for agents is the right move for the next wave of software.
The Stripe Projects example shows why. The agent can discover services through a catalog, provision Cloudflare resources, and use payment tokens without ever seeing raw card data. That is not just smoother. It is structurally better than the old model, where the platform had to guess what the user wanted, then shove them through half a dozen setup screens. Standardized orchestration makes the ecosystem more legible to agents and less exhausting for humans.
The counter-argument
The strongest objection is obvious: giving agents the ability to create accounts and spend money sounds dangerous. A buggy prompt, a malicious instruction, or a confused user could trigger unwanted purchases, domain registrations, or account sprawl. There is also a governance concern. If an agent can provision infrastructure on behalf of a person, where exactly does responsibility sit when something goes wrong?
That concern is real, and Cloudflare does not dismiss it. The system still requires human approval at key points, and payment is constrained by a default monthly spend limit. Raw card details are not exposed to the agent. Those are the right guardrails, and they prove the point: the answer is not to block agentic provisioning, but to design it with explicit authorization, bounded budgets, and auditable actions. The risk is manageable because the protocol separates identity, payment, and execution instead of collapsing them into one opaque agent action.
What I reject is the idea that risk justifies preserving the old manual workflow. Manual setup is not safer by default. It is merely familiar. Humans already make expensive mistakes with billing, permissions, and domain purchases, and they do it more slowly. A well-designed agent flow with limits, consent, and logging is safer than a scattered process where users paste tokens into random tools and hope they remembered every step.
What to do with this
If you are an engineer, stop treating provisioning as a separate product surface and start designing it as part of the agent journey. Build explicit catalogs, scoped credentials, budget caps, and consent checkpoints. If you are a PM or founder, focus on the first successful deployment, not the prettiest onboarding funnel. The winning platform will be the one that lets a signed-in user move from intent to production with the fewest irreversible choices, while still keeping the right approvals in place.
// Related Articles
- [IND]
Why Nebius’s AI Pivot Is More Real Than Hype
- [IND]
Nvidia backs Corning factories with billions
- [IND]
Why Anthropic and the Gates Foundation should fund AI public goods
- [IND]
Why Observability Is Critical for Cloud-Native Systems
- [IND]
Data centers are pushing homeowners to solar
- [IND]
How to choose a GPU for 异环