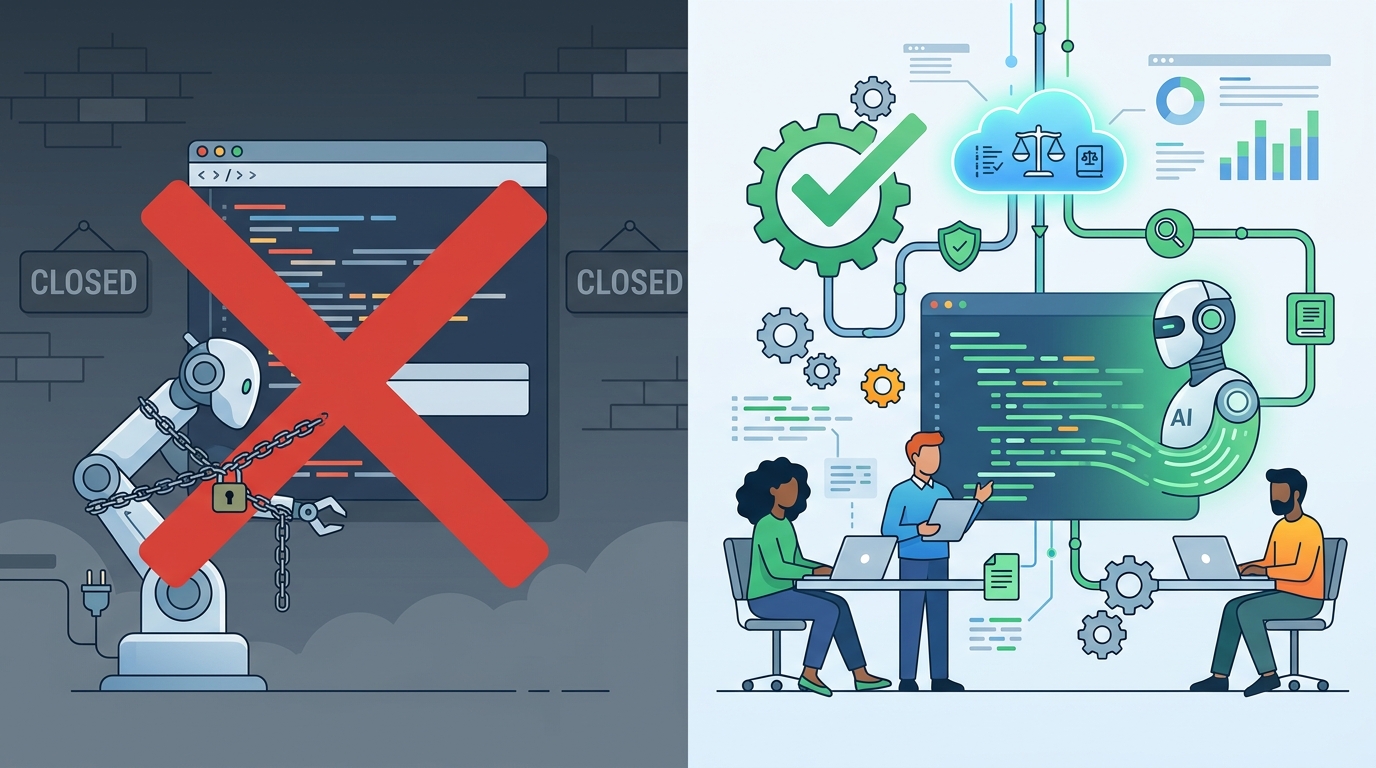
Why AI coding assistants need tighter governance, not blanket bans
AI coding assistants are worth using, but only inside stricter governance, review, and security controls.

AI coding assistants should be adopted only with stricter security governance and review controls.
I support AI coding assistants, but only if security gets veto power over how they are used.
I backed the rollout because the business case was obvious. Developers were drowning in repetitive work, deadlines were tightening, and technical debt was piling up in places leaders rarely see until it hurts. A coding assistant can draft tests, explain old code, suggest refactors, and help junior engineers move faster without waiting for a senior engineer to free up. Microsoft said 15 million developers were already using GitHub Copilot in 2025, which tells you this is no longer a novelty. The productivity gain is real, and pretending otherwise is how companies end up with shadow adoption and no control.
First argument: the productivity case is real, and it is not small
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
AI coding assistants remove the kind of work that drains teams without creating much value. Boilerplate, documentation drift, repetitive test scaffolding, and legacy code walkthroughs are exactly the tasks that slow delivery and wear down good engineers. When a tool takes over the first draft, senior developers spend more time on architecture and less time on busywork. That matters because software teams do not fail only from bad ideas. They fail from accumulated friction.
The strongest evidence is not hype, it is adoption. GitHub Copilot’s scale shows that engineers are voting with their keyboards, not their slide decks. When millions of developers use the same class of tool, the question stops being whether the tool is useful and becomes whether the organization is mature enough to govern it. Refusing the tool does not preserve safety. It preserves inefficiency while people find ways around policy.
Second argument: the security risk is structural, not cosmetic
The security team was right to push back because the risk is not just that the AI writes a bad function. The real problem is that code output rises faster than review capacity. That creates a control gap. If a model suggests a dependency nobody intended, if a junior engineer pastes sensitive context into a prompt, or if generated code slips through because it looks polished, the organization now owns a faster path to the same old mistakes.
There is also a supply chain angle that security teams cannot ignore. Snyk described a February 2026 case in which a vulnerability chain turned an AI coding tool’s issue triage bot into a supply chain attack path. That is exactly the kind of example that makes the risk concrete. The issue is not theoretical model behavior. It is how quickly an AI-assisted workflow can widen the blast radius when provenance, logging, and dependency review are weak.
The counter-argument
The best case against my position is simple: AI coding assistants are already embedded in developer workflows, and adding heavy governance slows teams down enough to erase the benefit. If every prompt needs scrutiny, every output needs extra review, and every use case needs approval, then the tool becomes a bureaucratic tax. Security teams already struggle to keep pace with cloud, identity, and supply chain risk. Asking them to police every AI-assisted change sounds like a path to bottlenecks and resentment.

That argument is strong, and it is why blanket bans are a bad answer. But the rebuttal is stronger: the choice is not between speed and control. It is between controlled speed and secret risk. If you do not define where the tool can be used, what data it can see, which code paths are off-limits, and what evidence is required before merge, developers will use it anyway. The result is not faster delivery with fewer checks. It is faster delivery with invisible risk.
What to do with this
If you are an engineer, PM, or founder, treat AI coding assistants like a production system, not a perk. Approve low-risk use cases first, such as test generation, documentation help, and code explanation. Keep them out of secrets handling, auth flows, encryption logic, regulated data paths, and sensitive infrastructure code unless you have explicit review rules. Require prompt hygiene, dependency scanning, logging, and real human sign-off. Most important, put security in the design process early. If governance arrives after adoption, you are not managing AI-assisted development. You are negotiating with it.
// Related Articles
- [IND]
Why Nebius’s AI Pivot Is More Real Than Hype
- [IND]
Nvidia backs Corning factories with billions
- [IND]
Why Anthropic and the Gates Foundation should fund AI public goods
- [IND]
Why Observability Is Critical for Cloud-Native Systems
- [IND]
Data centers are pushing homeowners to solar
- [IND]
How to choose a GPU for 异环