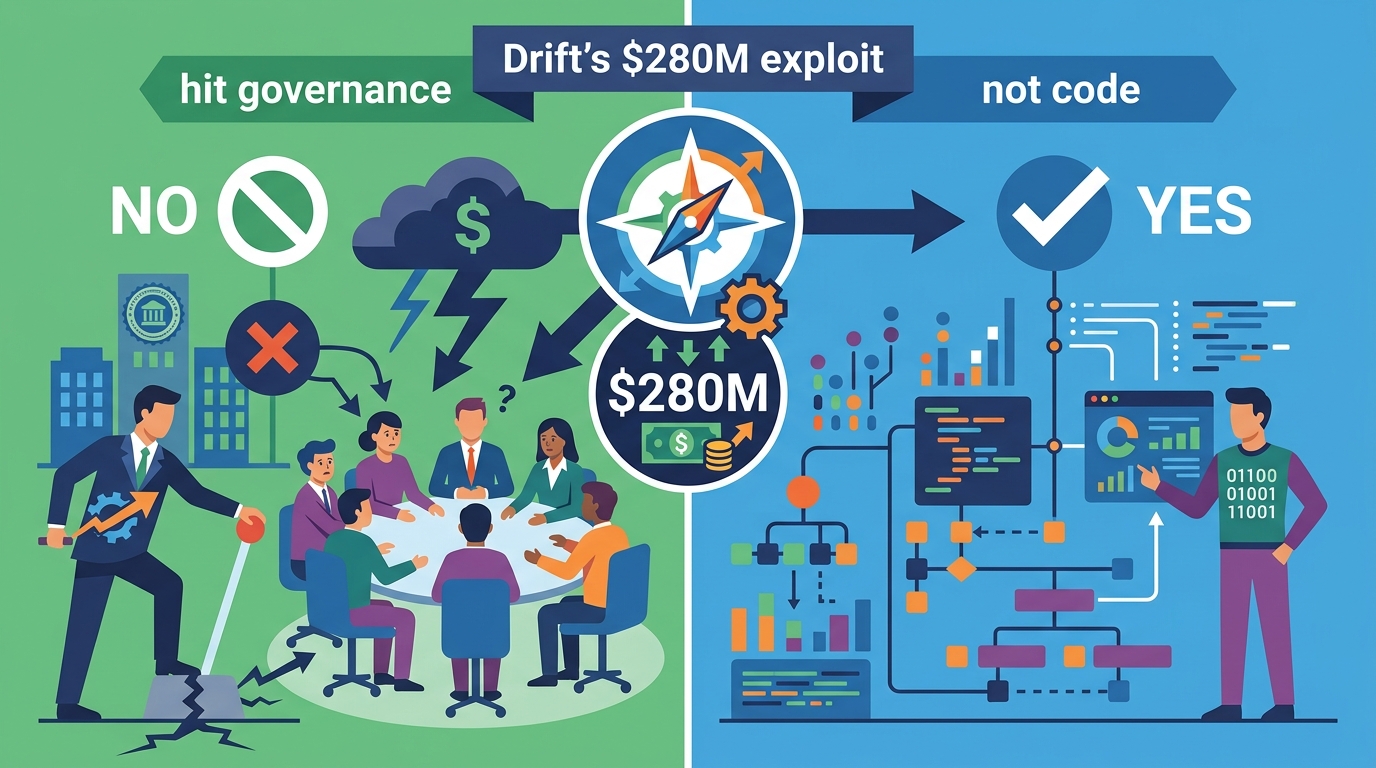
Drift’s $280M exploit hit governance, not code
Drift Protocol lost about $280M after attackers abused governance controls on Solana, exposing how DeFi failures can start with approvals.

Drift Protocol is dealing with an estimated $280 million exploit, and the part that should worry every DeFi team is simple: the attacker did not need to smash through the smart contracts. Instead, the breach targeted governance controls, approvals, and the messy human layer around them. On a network built for speed, that kind of attack can move from preparation to damage in minutes.
The incident, first described by Drift on X, appears to have unfolded over weeks before the final takeover. That timeline matters because it changes the usual security story. This was not just a bug hunt or a flash-loan stunt. It looks more like a patient operation aimed at the protocol’s administrative path, with durable nonces and multisig approvals used as the entry point.
How the attack appears to have worked
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
Drift is a Solana-based perpetuals trading platform, and like many DeFi systems it depends on a mix of onchain contracts and offchain coordination. In this case, the attacker allegedly gained enough control over the protocol’s durable nonce workflow and multisig approvals to push through admin actions.

That distinction matters. A contract exploit usually means a bad line of code or a broken assumption in the protocol logic. A governance compromise means the attacker found a way to convince, trick, or otherwise capture the approval process itself. Drift says there is no evidence of a smart contract bug and no sign that seed phrases were directly exposed.
Instead, the attack seems to have relied on pre-signed transactions and delayed execution. Durable nonces let a transaction be signed in advance and submitted later, which is useful for planned operations. It is also dangerous when an attacker can stage actions quietly and fire them when conditions are right.
- Estimated loss: about $280 million
- Attack surface: governance controls, not core contract logic
- Execution window: minutes, after weeks of setup
- Chain involved: Solana
- Control path: Security Council multisig and nonce accounts
The timeline shows careful preparation
The most unsettling part of Drift’s account is how deliberate the sequence looks. On March 23, four durable nonce accounts were created. Two were linked to multisig members and two were controlled by the attacker. That suggests the attacker had already secured some level of approval before the final strike.
By March 27, Drift carried out a planned Security Council migration tied to a member change. On the surface, that looks like routine protocol maintenance. In practice, it may have given the attacker another opening to re-establish access through the updated approval set.
Then on March 30, another durable nonce account was created under the updated multisig. Finally, on April 1, a legitimate test transaction ran, and about a minute later the attacker triggered two pre-signed transactions. That sequence is the part that should make operators in DeFi sit up straight. The attacker did not rush. They waited until the protocol itself created the conditions for a fast takeover.
Drift’s own description of the event makes the point clearly:
“This was a highly sophisticated operation that appears to have involved…” — Drift Protocol on X
That quote is incomplete in the public post, but the meaning is obvious: Drift believes the incident involved more than opportunistic theft. It was planned, staged, and timed around the protocol’s own control systems.
Why the losses spread so far
Once the attacker got admin-level access, the rest moved quickly. Drift says deposits across borrow and lend positions, vault deposits, and trading funds were affected. The attacker removed withdrawal limits and introduced a malicious asset, which opened the door to large-scale draining.
That is a classic pattern in admin compromise. Once the control plane is captured, the attacker does not need to keep exploiting the system one bug at a time. They can simply rewrite the rules, disable protections, and move funds out at speed.
Drift also said some assets were not affected. DSOL that was never deposited into Drift remained safe, including tokens staked to the Drift validator. The protocol’s insurance fund was being withdrawn and secured as a precaution. Those details matter because they show the exploit was broad, but not total.
- Borrow and lend positions were affected
- Vault deposits were exposed
- Trading funds were impacted
- DSOL outside Drift deposits remained safe
- The insurance fund was moved as a precaution
How this compares with other DeFi failures
DeFi has seen plenty of contract failures, but this one belongs in a different bucket. When Euler lost funds in 2023, the issue centered on a smart contract flaw that could be exploited through protocol logic. When Wormhole suffered its major exploit, the bridge’s verification model was the weak point. Drift’s incident points instead to approval control and operational trust.
That difference matters for builders because code audits alone do not cover the full risk picture. If a protocol depends on a small group of signers, a nonce process, or delayed transaction execution, then social engineering and process abuse become part of the attack surface. In other words, the weakest link may be the workflow around the contracts, not the contracts themselves.
Here is the practical comparison:
- Code exploit: attacker breaks protocol logic directly
- Bridge exploit: attacker abuses cross-chain verification or message handling
- Governance exploit: attacker captures approvals, signers, or admin paths
- Drift’s case: governance and administrative control appear to be the target
That is why this incident will likely matter beyond Solana. Any protocol that uses multisigs, delayed execution, or delegated admin rights now has another real-world example of how those systems can fail under pressure.
What happens next for Drift and DeFi teams
Drift says it has frozen remaining protocol functions, removed the compromised wallet from the multisig, and is working with security firms, exchanges, bridges, and law enforcement to trace the stolen assets. A full postmortem is expected in the coming days.
The bigger lesson is not hard to see. DeFi teams need to treat governance like production infrastructure, because that is what it is. If approvals can be misrepresented, if nonce workflows can be staged in advance, or if signer rotation creates a blind spot, then the protocol is exposed even when the contracts are fine.
My read is that this case will push more teams to tighten signer policy, shorten approval windows, and add more friction to admin actions that can move large sums. The next question is whether users will start demanding proof that a protocol’s control plane is as tested as its code. If they do, Drift’s $280 million loss may become the example that changes how DeFi thinks about trust, not just security audits.
// Related Articles
- [IND]
Why Nebius’s AI Pivot Is More Real Than Hype
- [IND]
Nvidia backs Corning factories with billions
- [IND]
Why Anthropic and the Gates Foundation should fund AI public goods
- [IND]
Why Observability Is Critical for Cloud-Native Systems
- [IND]
Data centers are pushing homeowners to solar
- [IND]
How to choose a GPU for 异环