Why AWS’s repository-wide security scanner matters more than faster S…
AWS Security Agent’s full-repository scan is a better security model than pattern-based SAST.
AWS Security Agent’s full-repository scan is a better security model than pattern-based SAST.
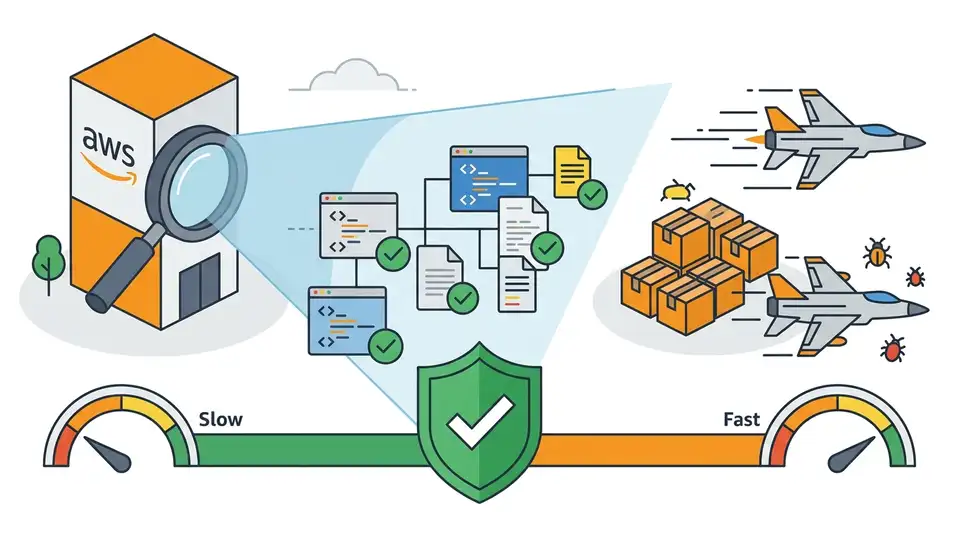
AWS is right to push full-repository code scanning because the bugs that hurt teams most are architectural, not local, and pattern-based SAST keeps missing them.
In its preview announcement, AWS describes findings that go beyond a single sink or tainted variable: a validation function that misses single quotes across five regex profiles, a stored procedure that bypasses that validation entirely, and an XSS issue where one path uses Encode.forHtml() while another path in the same file does not. Those are not toy examples. They are the exact kind of cross-file, cross-flow failures that force security teams to read whole systems, not just lines of code. A scanner that profiles trust boundaries, data flows, and authorization invariants before it hunts for bugs is aimed at the right target.
Security failures are usually systemic, not local
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
The first reason this matters is simple: the most damaging flaws in modern applications are rarely isolated syntax mistakes. They are gaps between components, assumptions that do not hold across services, and authorization logic that breaks in one branch while working in another. AWS’s own example of inconsistent HTML encoding in one context but not another shows why line-by-line tools fall short. The presence of a safe function does not make the application safe if the dangerous path sits beside it.
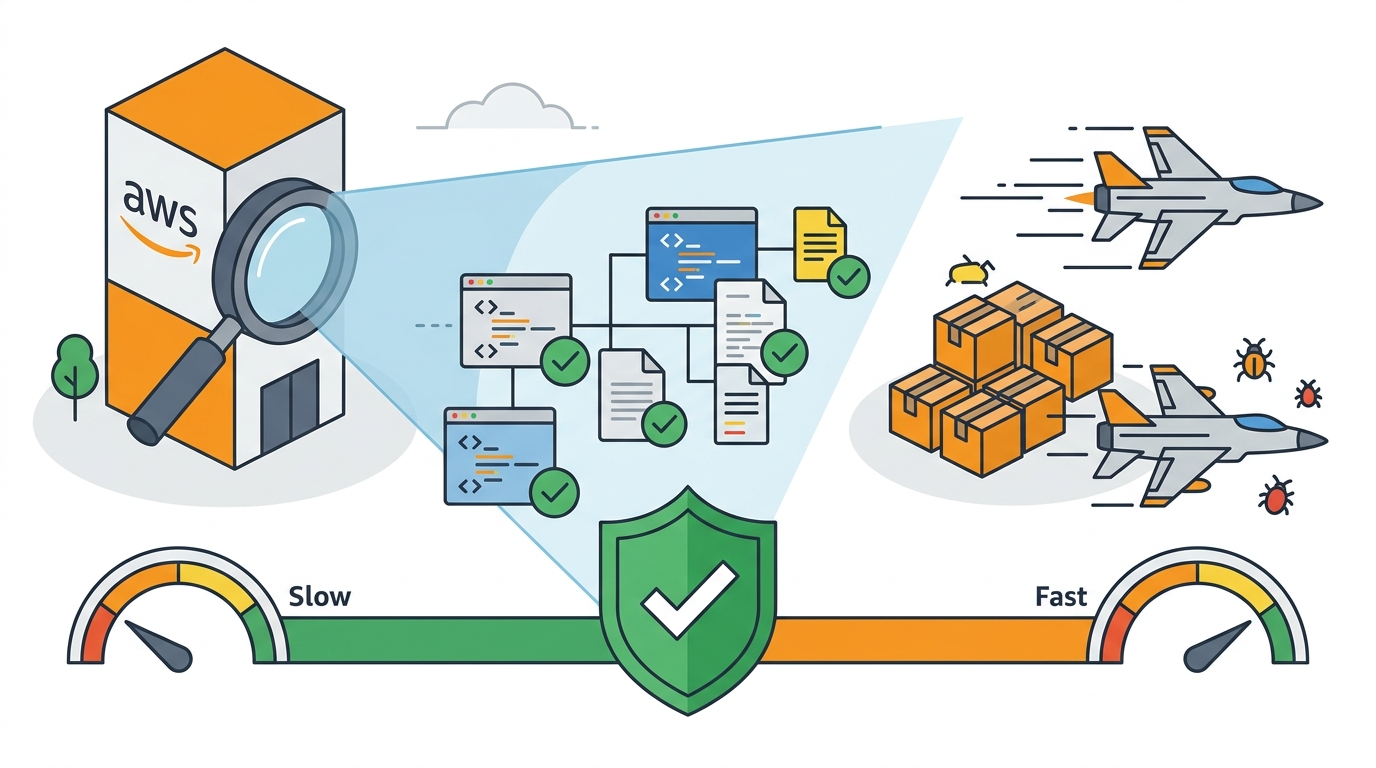
This is where full-repository analysis earns its keep. By reading the whole code base and building a security model first, AWS Security Agent can connect the dots between entry points, defenses, and data flow. That is the difference between flagging a suspicious call and explaining why a specific route, procedure, or trust boundary creates exploitable behavior. For engineering teams, that shift matters more than raw scan speed.
Context beats pattern matching
Traditional SAST tools are good at what they were built to do: catch known patterns fast. They are useful for obvious issues like an unescaped output, a hard-coded secret, or a direct SQL injection sink. But the AWS post makes the central argument against them plain. A tool that only matches code against signatures cannot tell you that a validation layer misses one case out of five, or that another stored procedure skips the validation layer entirely. That is not a pattern problem. It is a reasoning problem.
The store-procedure example is the strongest evidence in the announcement. AWS says the scanner did not stop at the EXECUTE IMMEDIATE call. It traced the validation function, named all five regex profiles, explained why single quotes mattered for that database engine, and found the bypass in another procedure. That is exactly what a human security researcher does when they are serious. If a tool can surface the systemic gap instead of the local symptom, it saves teams from patching the wrong thing.
Transparent uncertainty is a feature, not a weakness
The second reason to take this seriously is that AWS is not pretending the scanner has perfect knowledge. Each finding is split into verified evidence and could-not-verify context, with separate severity and confidence ratings. That is a better contract than the usual security output, which often buries uncertainty inside a single alert and leaves developers guessing whether the issue is real, theoretical, or environment-dependent. A scanner that says what it proved and what it inferred is easier to trust.

This matters because security work is full of deployment-specific conditions. Network segmentation, runtime controls, and authorization middleware can change whether a code flaw is exploitable. AWS’s structure acknowledges that reality instead of flattening it. The result is a finding format that is more useful for triage: developers can see the problem, the impact, the evidence, and the remediation without having to reverse-engineer the scanner’s logic. That is a better workflow for busy teams and a better signal for security leads deciding where to spend human review time.
The counter-argument
The strongest objection is that AI-driven scanning will produce noise, overreach, and false confidence. Security teams have seen “smart” tools that promise deep reasoning and deliver a flood of vague findings. They also know that a model can infer an attack path that looks persuasive but collapses under deployment realities. In that view, classic SAST remains safer because it is narrower, more deterministic, and easier to audit.
That concern is real, and AWS does not erase it. But it is not a reason to stay with pattern matching as the primary defense. The post’s validation stage is specifically designed to counter hallucinated certainty: every candidate is independently re-read, argued both ways, and rejected only when the evidence against it is as strong as the evidence for it. The tool is also framed as complementary to existing security tooling, not a replacement. That is the right boundary. Use deterministic tools for deterministic checks, and use repository-wide reasoning for the design-level issues deterministic tools miss.
What to do with this
If you are an engineer or security lead, treat repository-wide scanning as an upstream review layer, not a last-mile checkbox. Run it before pen tests, before major release gates, and when you inherit unfamiliar code. Use it to find the cross-file logic bugs, inconsistent encodings, and authorization gaps that static pattern matching overlooks. Then force every high-severity finding through a human review that checks deployment assumptions, because the goal is not to replace judgment. The goal is to spend human judgment where it matters most.
// Related Articles
- [TOOLS]
Vibe Research: AI Tools for Faster Research
- [TOOLS]
Why Docker’s microVM sandboxes are the right move for AI agents
- [TOOLS]
Why Gemini API pricing is cheaper than it looks
- [TOOLS]
Why VidHub 会员互通不是“买一次全设备通用”
- [TOOLS]
Why Bun’s Zig-to-Rust experiment is the right move
- [TOOLS]
Why OpenAI API pricing is a product strategy, not a footnote