Cloudflare Mesh brings private networks to agents
Cloudflare Mesh turns Cloudflare One into a private network for users, devices, and AI agents, with 50-node free tier support.

Cloudflare Mesh adds private-network access for users, devices, and AI agents inside Cloudflare One.
Cloudflare announced Cloudflare One Mesh on 2026-05-08, and the pitch is simple: stop treating AI agents like a special network problem. Instead of bolting on a new access stack, Cloudflare is extending the one it already sells for Zero Trust and SASE.
The company says Mesh starts with a free tier for 50 nodes and 50 users, routes traffic through Cloudflare’s network of 330+ cities, and ties directly into existing Gateway, Access, and device posture policies. That makes this less like a fresh product category and more like a new mode for the tools many teams already use.
| Item | What Cloudflare said | Why it matters |
|---|---|---|
| Free tier | 50 nodes and 50 users | Enough for a small team, lab, or staging environment |
| Global routing | 330+ cities | Traffic stays on Cloudflare’s backbone instead of ad hoc relays |
| Launch date | 2026-05-08 | Mesh is available now, not just on a roadmap |
| Identity model | Users, nodes, and agents | Policies can eventually follow the actor, not only the device |
Why Cloudflare thinks agents break the old model
Get the latest AI news in your inbox
Weekly picks of model releases, tools, and deep dives — no spam, unsubscribe anytime.
No spam. Unsubscribe at any time.
Cloudflare’s argument starts with a real shift in who talks to private infrastructure. A year ago, private access mostly meant developers SSHing into servers or services calling APIs. Now the client can be an AI coding assistant, a home assistant running on a Mac mini, or a worker that needs to query an internal database without exposing it to the public internet.
That matters because the old tools were built for humans. VPNs assume interactive login. SSH tunnels need manual setup. Public endpoints make access easy, but they also widen the blast radius when something goes wrong. Once an agent gets network access, you also want visibility into what it can reach and what it actually does.
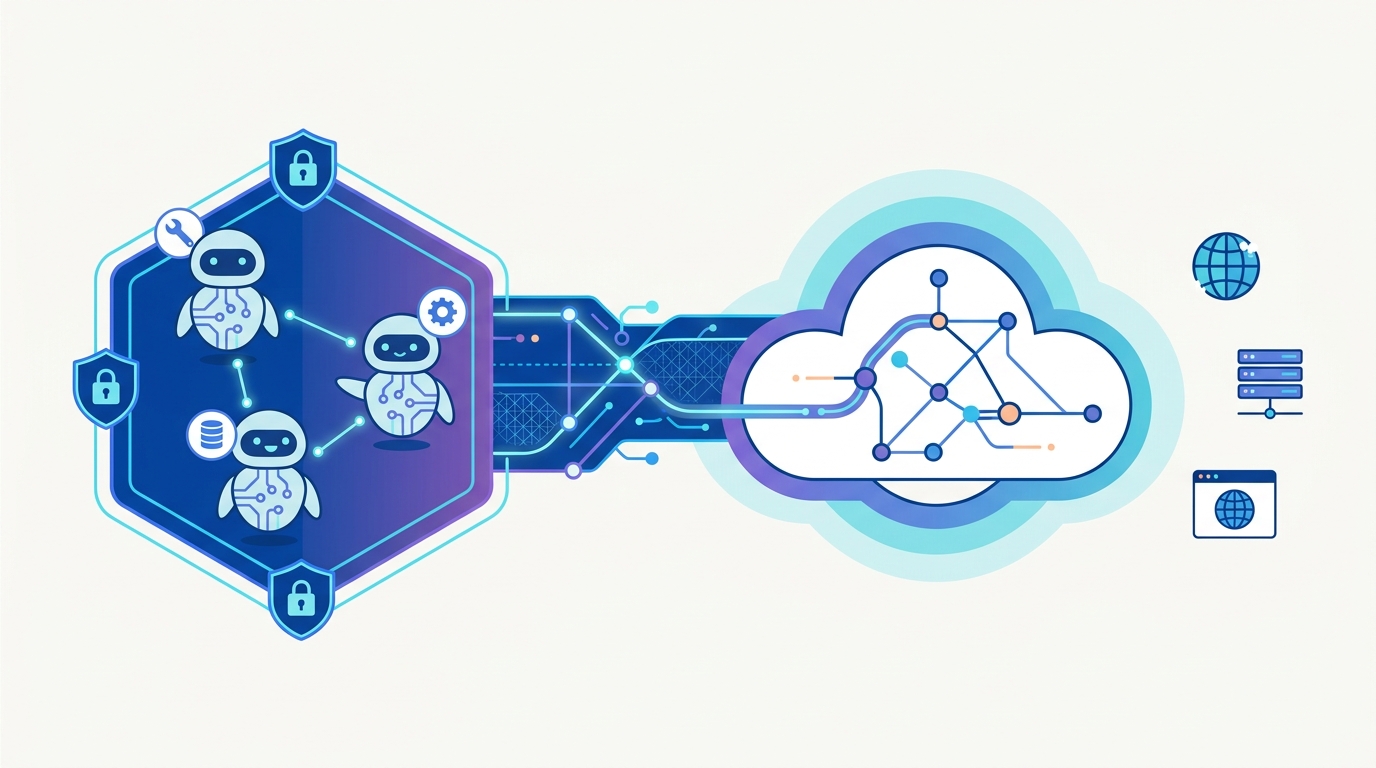
Cloudflare’s answer is Mesh: a private network layer that connects people, devices, servers, and agents under one policy system. The company says existing Cloudflare One controls apply automatically, including Gateway policy, Access rules, DNS filtering, and device posture checks.
- WARP Connector is now Cloudflare Mesh node.
- WARP Client is now Cloudflare One Client.
- Cloudflare Tunnel still fits one-way service exposure, while Mesh is for multi-party private networking.
Where Mesh fits in a real workflow
The easiest way to understand Mesh is to look at the use cases Cloudflare picked. In one example, a phone connects to a home lab running an AI assistant. In another, a laptop running Claude Code, Cursor, or Codex reaches staging databases and internal APIs. In a third, a deployed agent built with Cloudflare Agents SDK talks to private services from inside Cloudflare Workers.
Cloudflare is also trying to make the setup feel less like network engineering homework. The company says you can add one lightweight connector, assign a Mesh IP, and start routing private traffic in minutes. That is the product story here: fewer special cases, fewer one-off tunnels, and fewer reasons to expose internal systems to the open internet.
“You don’t need a new technology paradigm to secure agent workloads. You need a SASE built for the agent era, and that is Cloudflare One.”
Cloudflare, official Mesh announcement
The quote is doing a lot of work, but it also reveals the strategy. Cloudflare is not trying to sell Mesh as a separate network for agents. It is trying to make agents another class of endpoint inside the same Zero Trust policy engine that already handles employees and devices.
Mesh versus Tunnel: the difference is direction and shape
Cloudflare spends a fair amount of time separating Mesh from Cloudflare Tunnel, and that distinction is important. Tunnel is built for one-way access to a specific private service. Mesh is a multi-party network where nodes, devices, and applications can communicate with one another over private IPs.
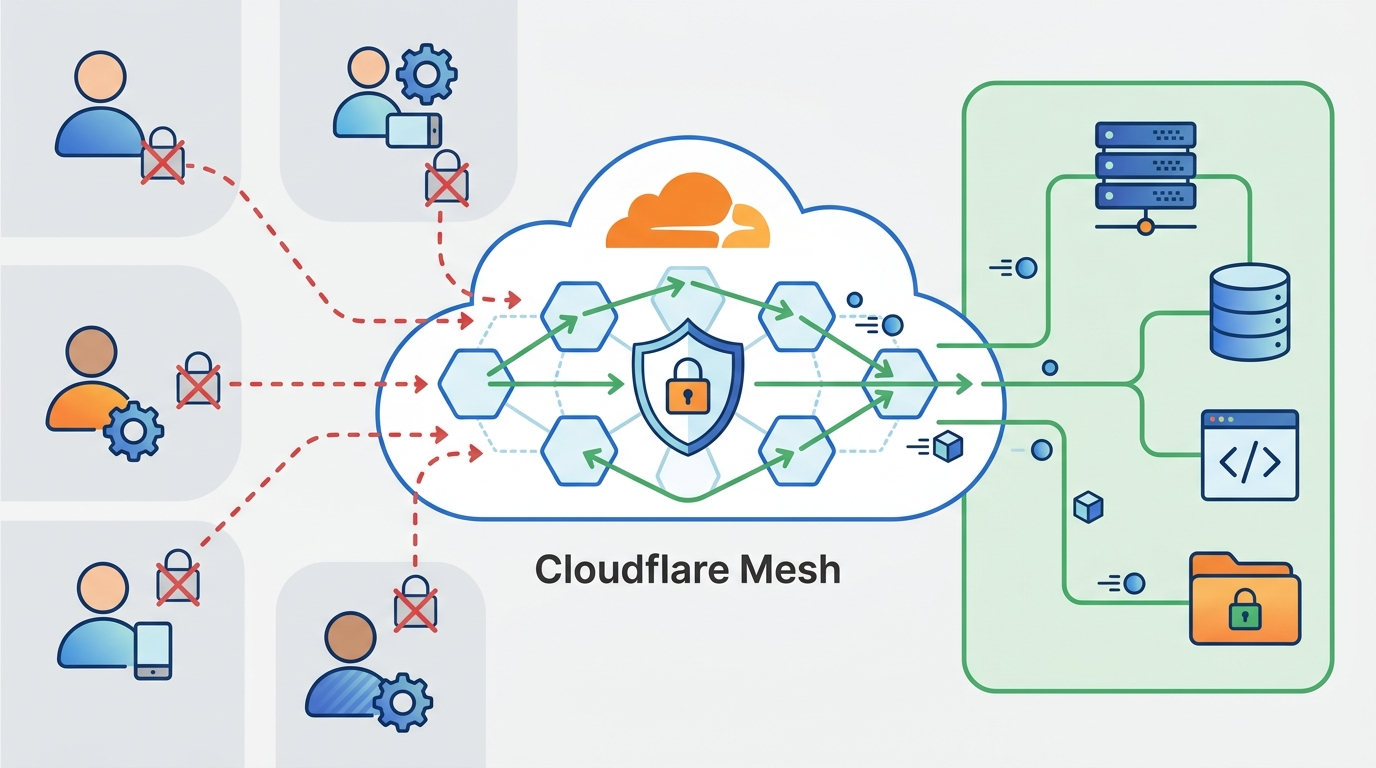
That difference changes how you think about setup. With Tunnel, you usually expose a service. With Mesh, you join resources to a network. If you have a laptop, a phone, a staging cluster, and a worker-based agent, Mesh lets them all live in the same private address space without hand-building a separate path for each connection.
Cloudflare also argues that routing through its backbone avoids the weaknesses of classic mesh networking over the public internet. NAT traversal is the usual pain point: when both ends sit behind NAT, direct peer-to-peer traffic often fails and falls back to relays. If those relays are scarce or far away, latency climbs and reliability drops.
- Mesh: many-to-many private networking.
- Tunnel: one service, one primary path, one-way exposure.
- Cloudflare backbone: global routing instead of scattered relay nodes.
- Policy inheritance: Gateway, DNS filtering, DLP, and Access can all apply to the same traffic.
There is also a practical business angle here. Cloudflare says the free tier includes 50 nodes and 50 users, which is enough to pull a small team, a test environment, and a few agents into the same fabric before anyone asks procurement for a bigger budget.
The roadmap says Cloudflare wants identity-aware routing
The current release is useful, but Cloudflare is clearly aiming beyond basic connectivity. The next set of features it outlined includes hostname routing, Mesh DNS, identity-aware routing, and a Docker image for container environments. Those additions matter because most teams do not think in IP addresses anymore. They think in service names, workloads, and permissions.
Hostname routing should let Mesh nodes serve names like wiki.local or api.staging.internal without managing address lists by hand. Mesh DNS would give every device and node a routable internal name such as postgres-staging.mesh. Identity-aware routing goes further by attaching the actor to the request, so policy can distinguish between the human who approved an action and the agent that executed it.
That last piece is the one to watch. If Cloudflare gets it right, a policy could allow Nikita’s deployment agent to read status, while requiring Nikita personally to approve writes. That is a cleaner model than IP-based rules, and it maps much better to how agentic systems actually work.
- Hostname routing reduces IP management for dynamic infrastructure.
- Mesh DNS gives internal services human-readable names.
- Identity-aware routing could separate the approver, the agent, and the scope.
- Docker support would bring Mesh into Kubernetes, Compose, and CI runners.
My read: Mesh is less about inventing a new network and more about making private access usable for the AI systems teams are already building. If Cloudflare ships the identity layer it describes, the most interesting question will not be whether agents can reach private services. It will be whether your policy engine can finally tell which agent did what, and why.
For teams already on Cloudflare One, the next move is obvious: test Mesh on a staging environment, then see whether your current Gateway and Access rules behave the way Cloudflare claims. For everyone else, the real test is simpler. Can a private network for agents stay understandable once the first dozen workloads, users, and approval flows pile in?
// Related Articles
- [TOOLS]
Why VidHub 会员互通不是“买一次全设备通用”
- [TOOLS]
Why Bun’s Zig-to-Rust experiment is the right move
- [TOOLS]
Why OpenAI API pricing is a product strategy, not a footnote
- [TOOLS]
Why Claude Code’s prompt design beats IDE copilots
- [TOOLS]
Why Databricks Model Serving is the right default for production infe…
- [TOOLS]
Why IBM’s Bob is the right kind of AI coding assistant